This blog post shares one of the Android application security vulnerability we discovered around a year back in 2014. Attify has been in business for the last couple of years, and the fact is not a lot has changed in the Android App Security since then.
Even though there have been numerous platform security improvements along the Android development curve, application developers tend to make the same mistake again and again.
Here at Attify, we review a lot of Android applications security vulnerabilities. Read more about Android application pentesting services here.
What is Vine
Vine is an application by Twitter, with which you can record and share short video clips.
What was the Android Application security vulnerability
The vulnerability falls in the category of **Insecure Data Storage in Mobile apps **for Android Application Security which has been categorised in OWASP Mobile Top 10 – M2 .
When you record videos, Vine application stores it on the device. And since it immediately posts it to the server, it deletes the local instance. Looks pretty good so far.
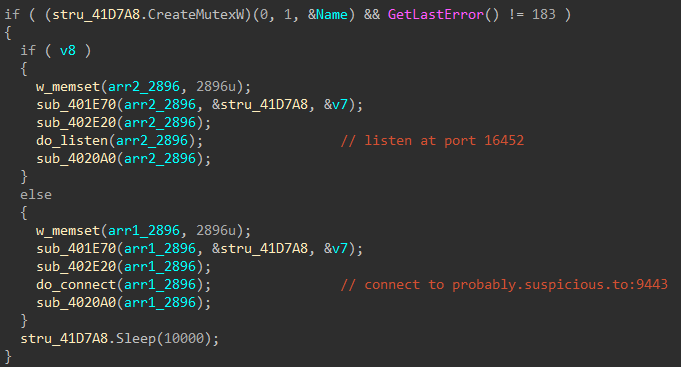
However, in between the time you record the video and Vine publishes it online, it’s stored on the device in SDCard or the External Storage. The file permissions for this file being stored in the external storage is world readable and writeable.
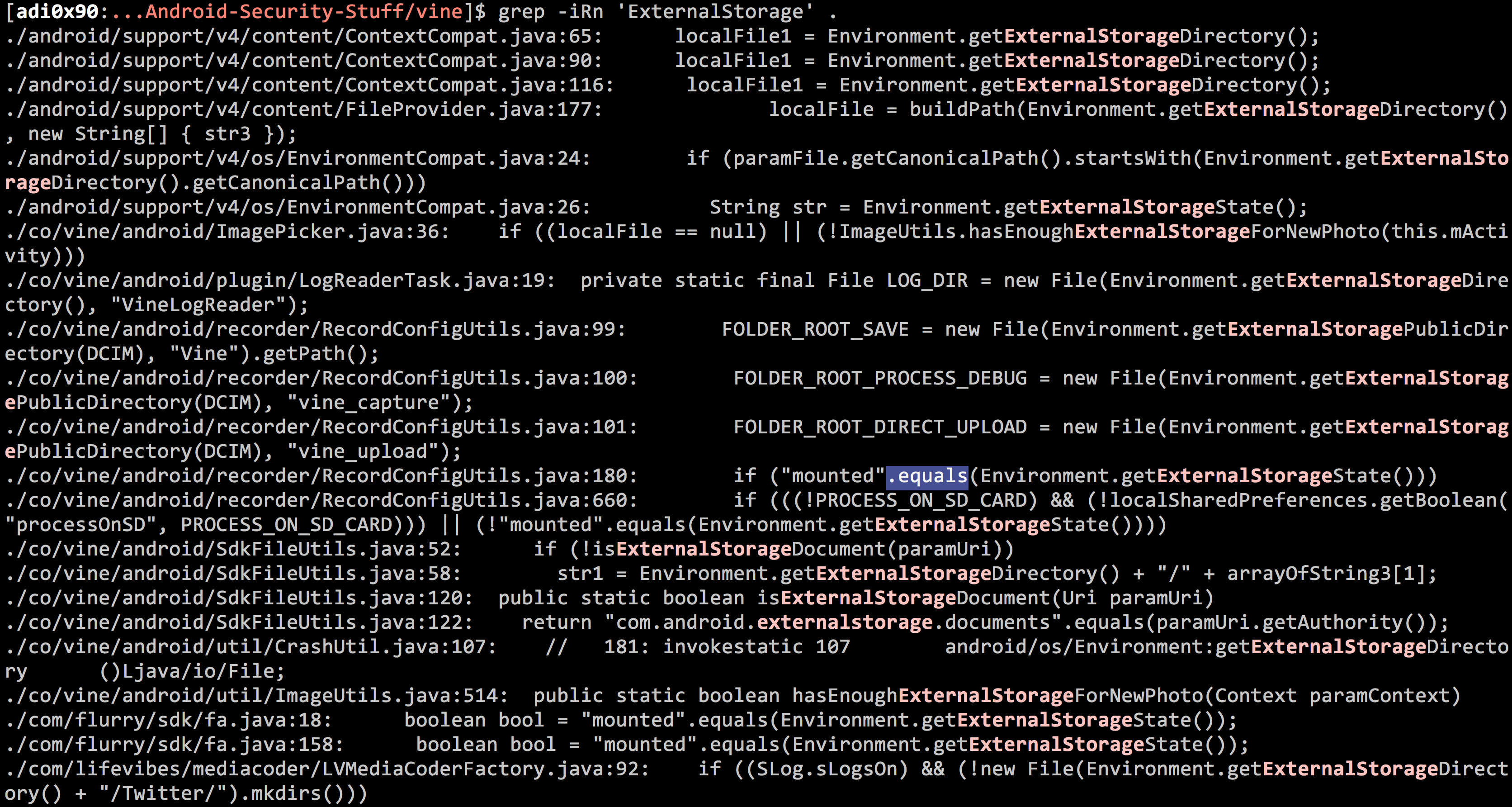
A quick search for ExternalStorage leads you to several instances of it being used, which when looked deeper would resolve to how the application is storing the file temporarily on the SDCard.
We identified it both automatically using using AppWatch as well as using hooking for the file system r/w.
Reporting the vulnerability to Twitter
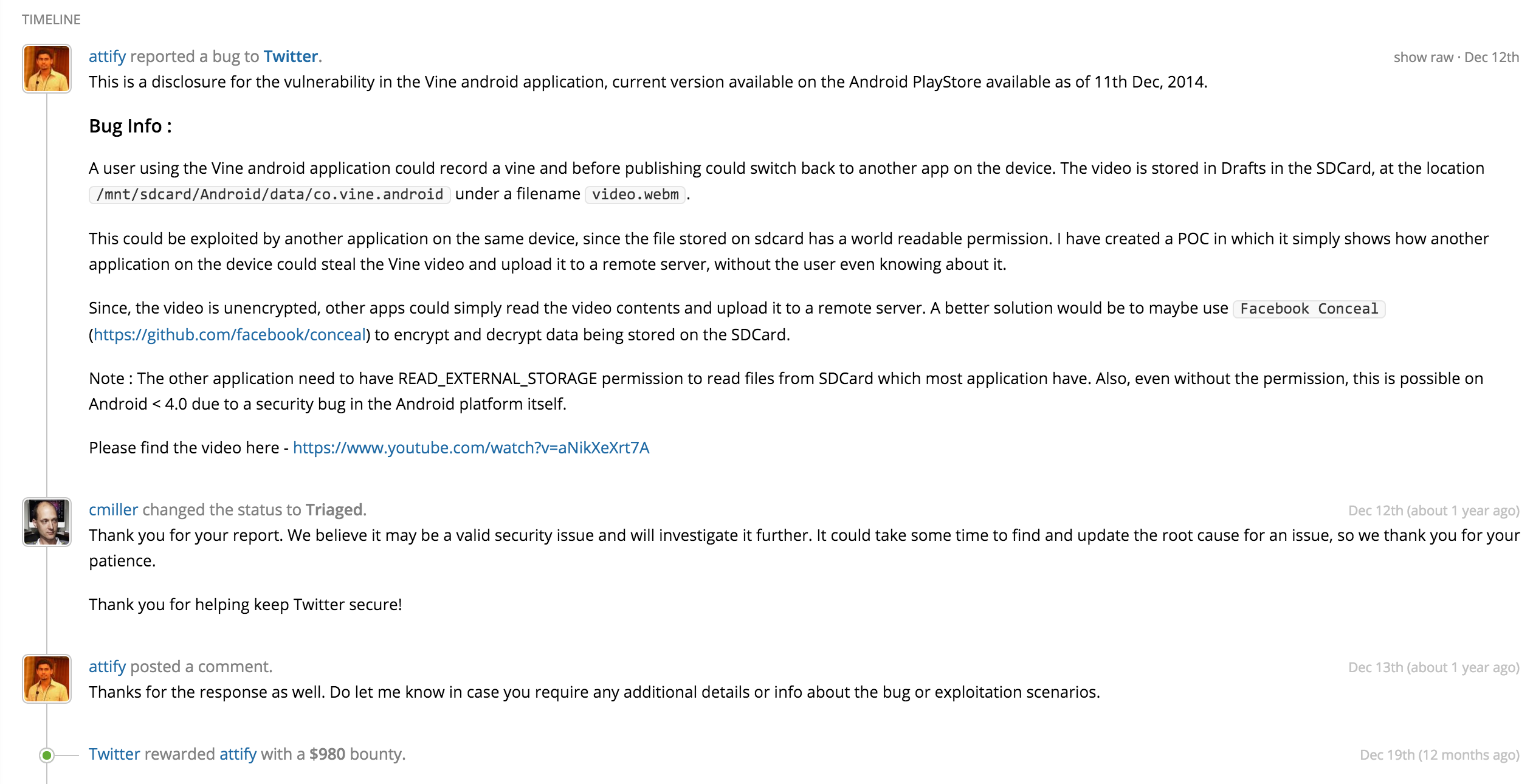
I reported the Android application security vulnerability to Twitter using HackerOne platform – which was my first and only encounter of the Hackerone platform (since I no longer do bug bounties). I found the platform to be really nice and easy to use. Charlie Miller reviewed my bug and paid us a bounty of $980 for this one.
Below is a screenshot of the conversation :
Find the POC explaining the vulnerability below :
[embedyt] http://www.youtube.com/watch?v=aNikXeXrt7A[/embedyt]
We will cover more instances of Insecure Data Storage in Android apps in one of our upcoming blog posts. But this post should serve as a good example of how **not **to store any sensitive data on the file system.
We are conducting Android and iOS Application security training at different locations in US, Australia, Netherlands, UK and UAE. Register for a live Mobile Application Security and Exploitation training at your organisation by contacting us here or sending us an email at secure [at] attify.com .
[contact-form to=’adi@attify.com’ subject=’Security Training Query’][contact-field label=’Name’ type=’name’ required=’1’/][contact-field label=’Official Email’ type=’email’ required=’1’/][contact-field label=’Query regarding training or pentesting services’ type=’textarea’ required=’1’/][/contact-form]