Welcome to the SMART HOME era! The Internet of Things is growing at a tremendous pace and is reaching new heights in every domain. At this point when a decent smart home can be had for under $500 rather than $1,200, the idea isn't just innovation and accommodation for early adopters — it's for EVERYBODY. Be it smart surveillance cameras, light bulbs, thermostats, or smart refrigerators—home automation gives us time to accomplish more essential things (or perhaps, just waste more time binging on Netflix 😉).
With the IoT space growing at such an unthinkable pace , the Internet of Things may soon be as indispensable as the Internet itself and its future scope is much larger than the fastest trillion dollars hitting - smartphone market.
While we’re readily adopting these IoT enabled technologies that seem to make our lives easier, how often do we wonder - what could go wrong?
Our dependence on connected devices has grown faster than the means to secure it. Because of the sheer scope of the IoT industry, companies rush products to market without basic built-in security measures. With the large number of vulnerable devices reaching the market, imagine the amount of data that is being and possibly could be exploited. As more advanced technologies come to the fore, over time, attackers have also come up with newer and more potent ways of exploiting our devices and invading our privacy.
Don’t worry, the existing threats from attackers should not deter you from using your gadgets. You should however, take concrete steps in order to keep your devices as secure as possible. Since a large number of devices already reach the market with a fair share of vulnerabilities, you, as an IoT user, need to be extra cautious and be mindful of the way you set up and utilize your gadgets.
Here are a few things to remember while ensuring your privacy and assessing your connected devices.
Better safe than sorry.
Information is a goldmine for cybercriminals, so it's time we begin securing our gadgets by any methods conceivable. Increased security awareness is the initial move towards battling IoT dangers.
IoT security is a mutual duty. Cautiousness and planning are the ideal approaches to remain ahead. Both manufacturers and end users should take appropriate measures to ensure remaining protected and limit security slips. The ideal way to affirm your smart home as "security smart" is to bring matters into your own hands.
Regardless of whether you utilize one brilliant gadget or a handful, improve the security of all your devices with these security tips:
Security monitoring
Consider purchasing devices offered only by reputable vendors that build in security features right from the start. Confirm that the vendor utilizes some sort of software-advancement life cycle program. As a manufacturer of IoT products, creating a threat-model in the very start should be absolutely mandatory. Security must be incorporated during design phase rather than adding it after the products have been developed and deployed. If not done at this stage, heftier costs will be incurred at a later stage.
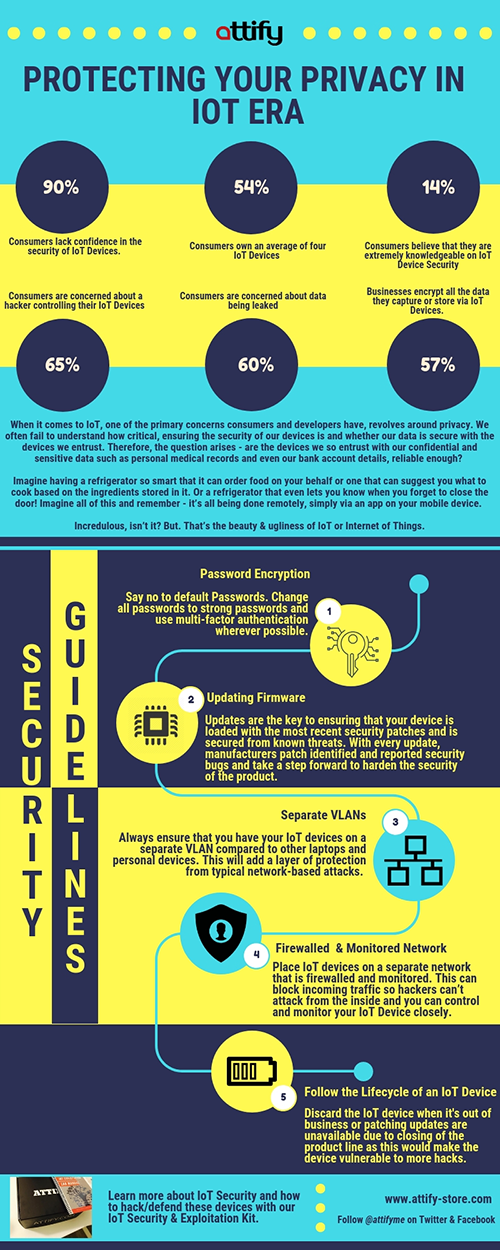
Say No to Default Passwords
One of the most important things to do is to change the default password upon first usage of any device. Make one of a kind/unique profiles for each IoT device you use. Be a smart user by using strong credentials and including the use of alphanumeric and special characters in your passphrase. Accounts with simple passwords are extremely easy to crack and break-into for malicious hackers.. Also, indulge in the habit of changing passwords on a regular basis. Always abstain from using a predictable password for IoT devices or the associated online accounts.
Control Over Your Data
It is vital to be aware of the manufacturers' Terms of Service and Privacy and Data Retention Policy prior to purchase. Buy from companies that are focused on securing your personal information. Ensure whether you as a consumer can control how your information is utilized & verify the accuracy of your data. With EU's GDPR coming into force on 25 May 2018, a user consent is required when personal data is being processed. It also provides consumers the right to withdraw their consent and get their information expelled through a "right to be forgotten" mechanism.
Avoid a hostile environment
Place smart devices in secure spaces, for example, inside a bolted area rather than outside, if possible. Search for a packaging furnished with an alarm to be alerted in case of potential tampering and weather damage. Ensure that the device has a strong fail open mechanism. Leverage tamper-resistant modules that will offer confirmation of endeavoured physical assaults. Check for build-in remote monitoring and device locking or wiping feature in case a failure/misuse is detected.
Set limits
An IoT device must perform reliably for the end goal to be of significant worth to the purchaser. Make sure you comprehend what capacities your IoT device has. For instance, some savvy smart TV can tune in to your discussions. Impair these features to suit you as per your convenience. Additionally, review the security and privacy settings before you start using the device and configure it in a way best suited for you.
Regularly Install Updates
Always use the most recent firmware which ensures mitigation of known vulnerabilities. Flaws that are discovered after the product has been deployed can be addressed quickly through security upgradability, patching, and vulnerability management strategies. Make sure to patch your device with updates, as they are made available. It is equally important to remember not to completely rely upon the update cycle as that could risk your device being exposed to attackers. Check device manufacturers' websites for updates on a regular basis and search for arrangements that offer online updates. Turn on automatic updates, if they're accessible.
Wireless networks
Understand the nature of wireless networks and avoid connecting your device to unfamiliar ones. Check for Wi-Fi Protected Access (WPA2) encryption protocol (at a minimum) and whenever possible, use a strong firewall protection. Ensure all networks provide end-to-end encryption with mutual authentication. Create a separate VLAN where to connect your IoT devices to. Michael Horowitz has an in-depth article available here on how to setup VLANs on your home network to safeguard your home network from vulnerable IoT devices.
The Internet of Things enables you to enhance your home and streamline your living. While connected devices seem like a great idea and make our lives significantly simpler, it is our responsibility as a user to be aware of the risks.
The multitude of cyber breaches that we have been hit with over the last decade emphasize the imminent need for us to not just be aware but, also take active steps to contribute the most towards cyber security.
The Equifax data breach is an example of failure to update software components leading to a disastrous hack. Equifax systems & servers were exploited in mid-May through Apache Struts web-application vulnerability that was disclosed and had a patch available in March. The credit-reporting giant however, failed to defend the credentials & other personal data of 143 million people from being exposed even though the company had more than two months to follow the simple remediation procedure of applying the available patch.
Another most severe malware attack--The WannaCry virus, exploited older Windows OS versions shutting down over 200,000 systems in 150 different countries affecting hospitals to car manufacturers, banks, universities, and individual systems. Only the updated Windows OS were secure from the ransomware which again highlights the importance of keeping all your systems and software patched and updated.
While setting up all your favourite features may be your priority, it is vital that you devote time to expand the security of your IoT devices. Although you might experience a considerable measure of inconvenience to set up cutting-edge security, such security measures ensure the safety of your personal data and preserve the integrity of your Internet of Things gadgets for years to come. By taking preventive measures early, you can help forestall malicious attacks when it truly matters.