Mobile Applications are often insecure. There can be a lot of reasons leading to the vulnerabilities – the most common being developer mistakes.
So how do you ensure the apps you are developing are secure, and don’t have any serious security issues. A good starting point is the OWASP Mobile Top 10. Before launching the application on the Google Play Store or App Store, you should also conduct a thorough security assessment of the app by your internal security team or through an security firm with an expertise in Mobile Security – Attify.
We at Attify work with developers and organisations around the world, helping them secure their mobile applications and preventing them from getting hacked.
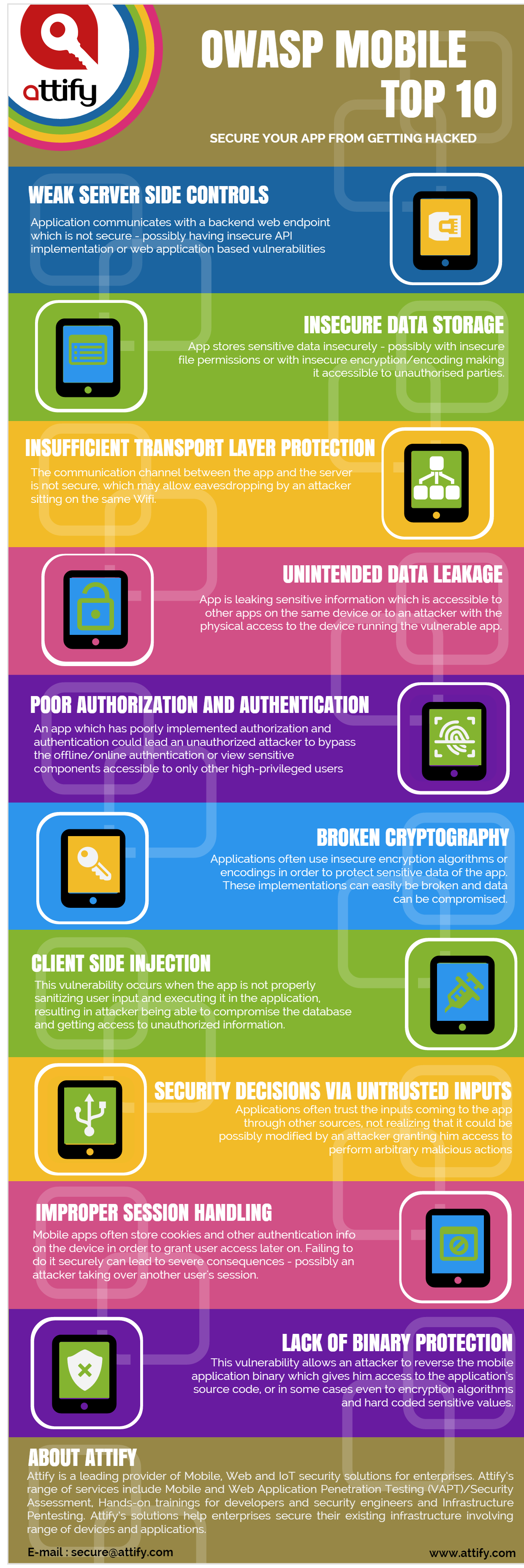
Below is the OWASP Mobile Security Top 10 vulnerabilities :
- M1: Weak Server Side Controls
- M2: Insecure Data Storage
- M3: Insufficient Transport Layer Protection
- M4: Unintended Data Leakage
- M5: Poor Authorization and Authentication
- M6: Broken Cryptography
- M7: Client Side Injection
- M8: Security Decisions Via Untrusted Inputs
- M9: Improper Session Handling
- M10: Lack of Binary Protections
We have described briefly about the individual categories in the below infographic.
Feel free to share the article with your folks to spread the awareness about Mobile Application Security.