Mobile Applications can have various type of security issues. We audit applications for security issues on a daily basis as a part of our Mobile Application Auditing services.
If you are a mobile application developer, here are quick 5 tips for you to ensure the security of your mobile app.
Secure IPC
In any mobile application, ensure that the components interacting with each other happens in a secure fashion. For ex, unauthorised access to the Activities, Services, Content Providers or any other component for that matter – should be secured. This can be done by ensuring that each of the component has been protected and also specified in the AndroidManifest.xml file.
Use encryption
Using encryption might sound a bit too generalised, but a lot of developers often forget to use it while working with sensitive data. Make sure that your application performs encryption of any sensitive data – whether in rest or transit. This will protect your application’s security, even if someone gets hold of the user’s device or gains access to it.
Secure Network Communication
Ensure that all the network communication which happens between the app and the web endpoint happens in a secure fashion. This means checking for any sensitive info leakage such as API keys from the network or making sure the communication happens over a secure channel. Also, ensure that your application performs proper SSL pinning.
Secure Data Storage
If you store users data on the device, ensure that it is stored with secure file permissions and encrypted. This applies to all the data – either stored in the application’s directory, external storage or any other location. Use secure libraries such as Facebook Conceal to enable fast and secure encryption and decryption of the data being stored.
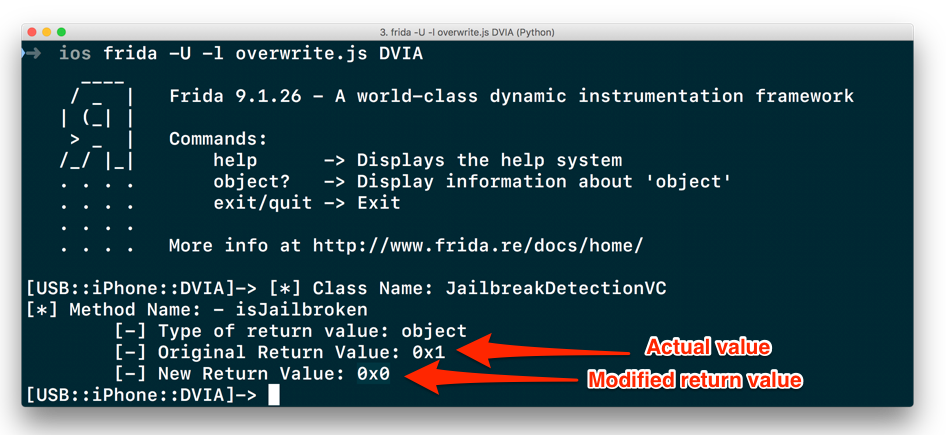
Binary Protection
Whichever platform you are using, attackers can reverse engineer your application and get to the app source code, which might reveal sensitive information. Ensure that your app uses proper obfuscation techniques – atleast to make it tough for the Reverse Engineers.
For any additional queries, or if you want Attify to help assess the security of your mobile application, get in touch with us over email – secure@attify.com .