There is an app for everything.
But the question is, are those apps trustworthy enough to put your personal information at risk.
Apps can range from the simplest ones like a Flashlight App to the highly complex Social Networking apps. Did you ever care to look at the permission of the app while installing? Or ever wondered to figure out why a flashlight wants access to your camera and internet.
Is an app acting as a backdoor to steal your personal information or Is the app in itself vulnerable, putting your sensitive information at risk. What if the vulnerable app is a banking application you use on a daily basis.
While companies today focus on delivering the best experience to the user, before their competitors, security is often an afterthought. Ask your App Developer, what is more valuable : Amazing Features or Security of your data. Often times, you won’t like what you hear from them.
I have been a developer in the past. And I know how great it feels to come up with a new app idea, convert it to reality and reach out to millions of users. The importance of security only gets realized when the app’s security is compromised and the data is leaked by the hackers. Too late to gain back the trust from your users.
So, we came up with a platform. A Platform, which can help you identify and secure your Mobile applications from being hacked. Sounds interesting?
Putting together years of Mobile Application Security Research, Attify has created AppWatch – an intelligent Mobile Application Security Platform, which automatically identifies security vulnerabilities in Mobile applications within a span of few minutes.
Here’s what you can do to get started in 3 simple steps :
Step 1. Sign Up
Sign Up for the AppWatch portal by clicking here :
The Signup process is quite straightforward. Just fill in your details and click on Submit.
Once done, you can then Login to AppWatch using your username and password.
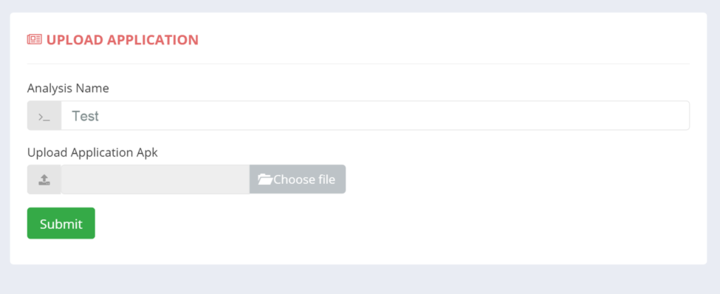
Step 2: Submit the App you want to scan
If you happen to have the app binary (mostly useful for developers), you can simply upload the APK in the section that says “Upload Application” .
OR, you can scan ANY app from the Google Play Store, by just searching for it as shown below.
Give it a Scan Name and you’re good to go.
As soon as you click the Submit button, AppWatch will start analyzing the application.
(Note : You’ll need credits to scan your application. One App Scan costs $1 as the part of promotional package)
Step 3: View your Report
Once the app has been scanned completely (which shouldn’t take more than 6 mins), you can check the report which will give you a detailed analysis of the vulnerabilities identified.
Below is how a sample report PDF looks like :
Be Secure and Start Scanning. 🙂