Attify is a leading provider for Mobile Application security for various organisations all over the world. We have got a number of requests to share the top secure coding guidelines for Mobile apps, so that developer can build much more secure applications.
So, we decided to write down the 10 Most important Secure Coding Guidelines for Mobile apps.
1. Protect Sensitive Data
Ensure that any data you store – on device or in the external storage is properly secured. You will need to take care of proper file permissions as well as the encryption of the data in case it’s sensitive.
2. Secure Authentication Credentials
Whenever you store the user’s credentials on the device ensure that the credentials are not leaked through cache, logs or any other medium. Advice the users to chose strong authentication credentials.
3. Data in Transit
For all the data in transit, ensure that all the communication is over a secure channel. If you are implementing SSL, ensure that SSL Pinning is in place – also securely implemented.
**4. Authentication and Session Management **
For Authentication and Session management, ensure that it can’t be spoofed in case of local authentication. In case of remote authentication, make sure that the data is securely communicated, and none of the sensitive authentication values are leaked via any medium.
5. Secure Services and Server
If you’re using APIs – REST or SOAP in your mobile app, ensure that the APIs does not contain any security issue or misconfiguration in the implementation. Here you should check the application for business logic flaws which could be triggered from the app. Securing the server is another important point which can be achieved by hardening the server, and implementing DDoS protection, port scanning detector, checking for outdated components, SELinux, Permission based vulnerabilities etc. (Infact, there are so many, we have build an entirely new training course on Infrastructure Security. Contact us at secure@attify.com for more details).
6. Secure 3rd party integration
If you are using any 3rd party component within your app, ensure that they don’t contain any security vulnerability in itself. A lot of times, vulnerable ad libraries or 3rd party SDKs end up making the entire app vulnerable.
7. Collect consent before collecting User Data
Whenever you are collecting any sensitive information about the user, ensure that the user is notified about it in advance. This way, you can reduce the risk of your company having bad reputation in terms of privacy violations.
8. Payment related security for Mobile Apps
If your mobile application contains payment or wallet functionality, you will need to pay special attention to those components. What we have seen over the past few years is, it is relatively easier to bypass and spoof payments on a mobile application, compared to web apps. Ensure that you have checks against attacks like bypassing payments, manipulating amounts etc.
9. Security updates
This is really essential if you have a mobile application. As soon as you come across any security vulnerability in your mobile app, ensure that a proper fix is rolled out to all the users running your app on their device. This will prevent users information being compromised, if the vulnerability is exploited in wild.
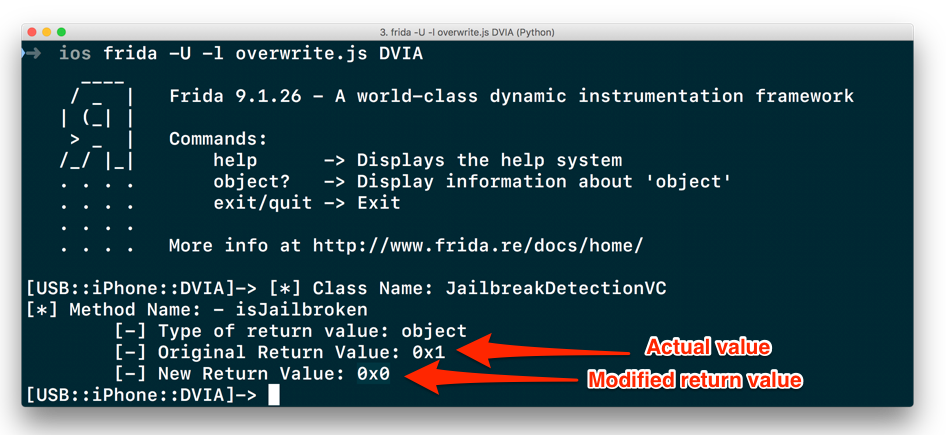
10. Safely use interpreters
Try not to use a lot of components or decisions based on runtime factors. Using method swizzling and other techniques, it is quite easy for an attacker to manipulate the run time variables and perform malicious actions.
Below is an infographic summarising the above points :
 Infographic on Mobile App Secure Coding Guidelines
Infographic on Mobile App Secure Coding Guidelines