Apktool is one of the de-facto tool for Android application reversing.
In the process of penetration testing at Attify, we faced an issue while reversing new Android apps. In most of the cases, the apps that were build using build-tools version 21.x raised few exceptions.
After a little research, we found that apktool was failing to decode arsc file because of large StringPools and even raised IO exception reading few header files.
The exception pointed to brut.androlib.AndroidlibException : Issue 664.
Well, this blog post is regarding how we solved the issue of apktool, so we won’t be discussing exceptions here in depth.
TL;DR
Without getting much into details of exception and issues, lets focus on how we solved it.
We built apktool from its source which is present at its official website. You can get the source code here.
**Following are the steps : **
-Download the source code and extract its content.
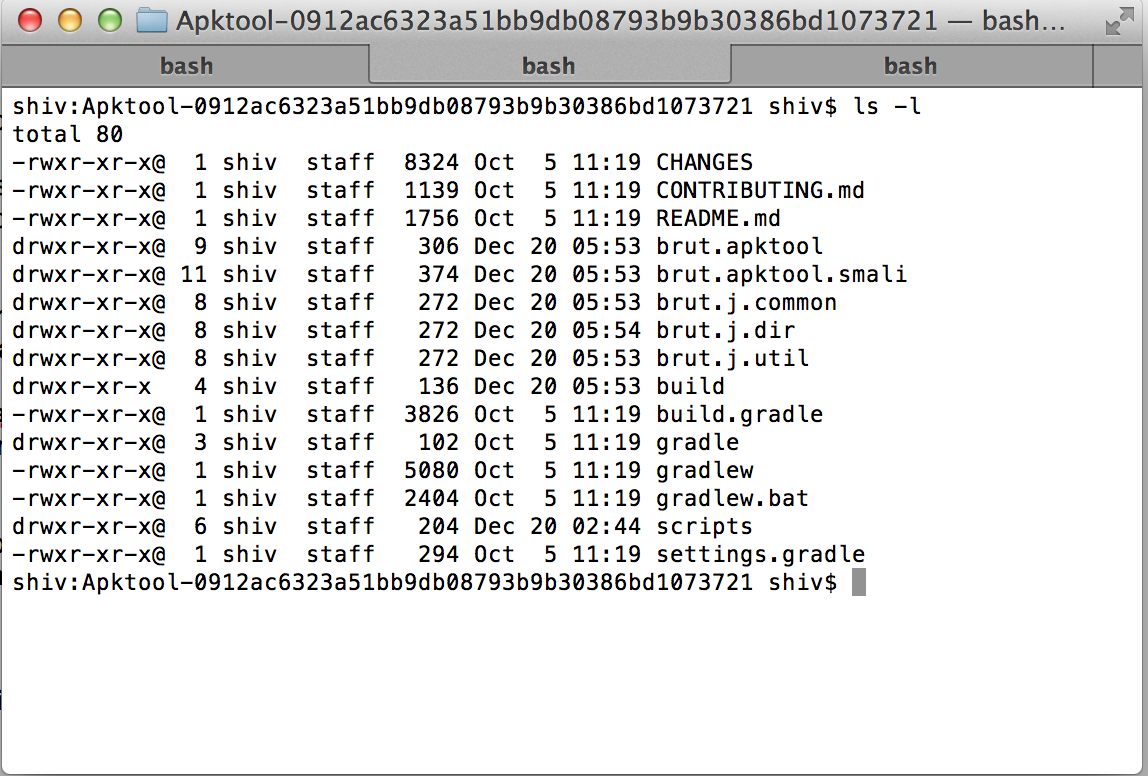
-Traverse into the extracted folder. The contents should be as shown below:
-Build source,
./gradlew build fatJar
Once the build is successful, traverse to libs folder
./brut.apktool/apktool-cli/build/libs/
-Rename the file from apktool-
-Give execute permission to apktool.jar
sudo chmod +x apktool.jar
-Place the apktool.jar to ‘bin‘ directory along with apktool config file. (Note: bin folder location may depend on operating systems used.)
For example, here is the command for Mac OS X.
sudo mv apktool.jar /usr/bin/
You can now continue to enjoy with your reversing and auditing fun. 🙂