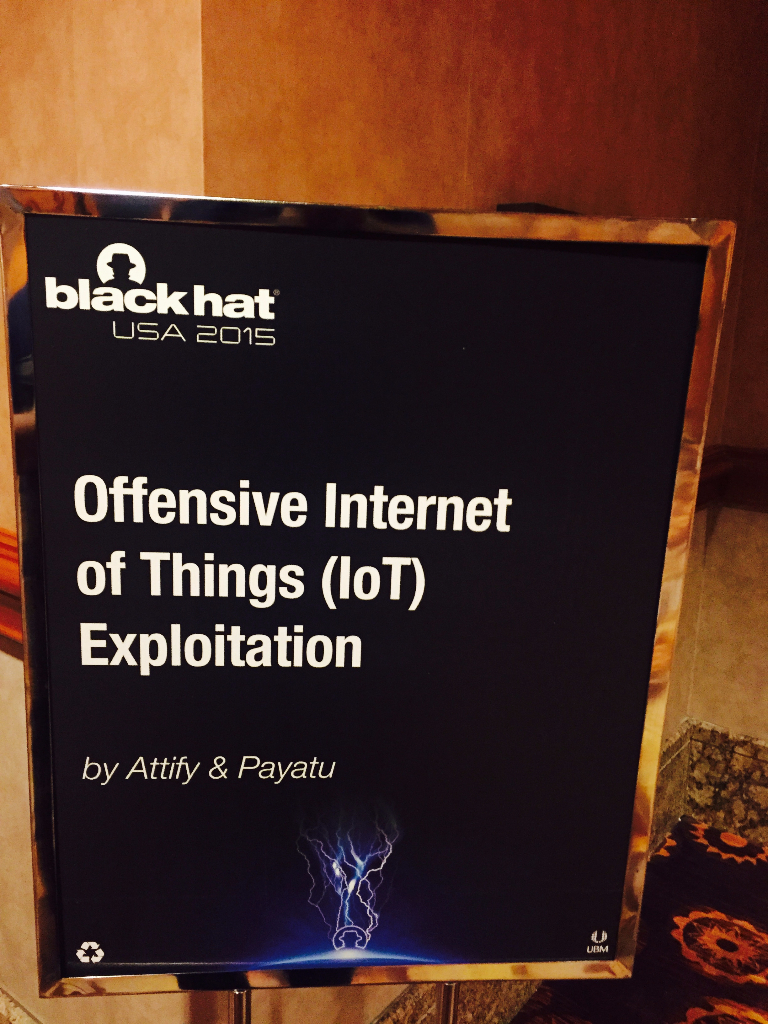
BlackHat 2015 was the first run of our IoT security training class named “Offensive Internet of Things Exploitation” and it was a HUGE success.
The class got sold out quite fast, much faster than we expected. In fact, we had to increase a few seats in both the batches of our class before limiting further registrations.
The training course was delivered by Attify’s founder Aditya Gupta and was an intensive 2-day hands-on class with lots of exercises and challenges to help attendees understand the security issues with the Internet of Things.
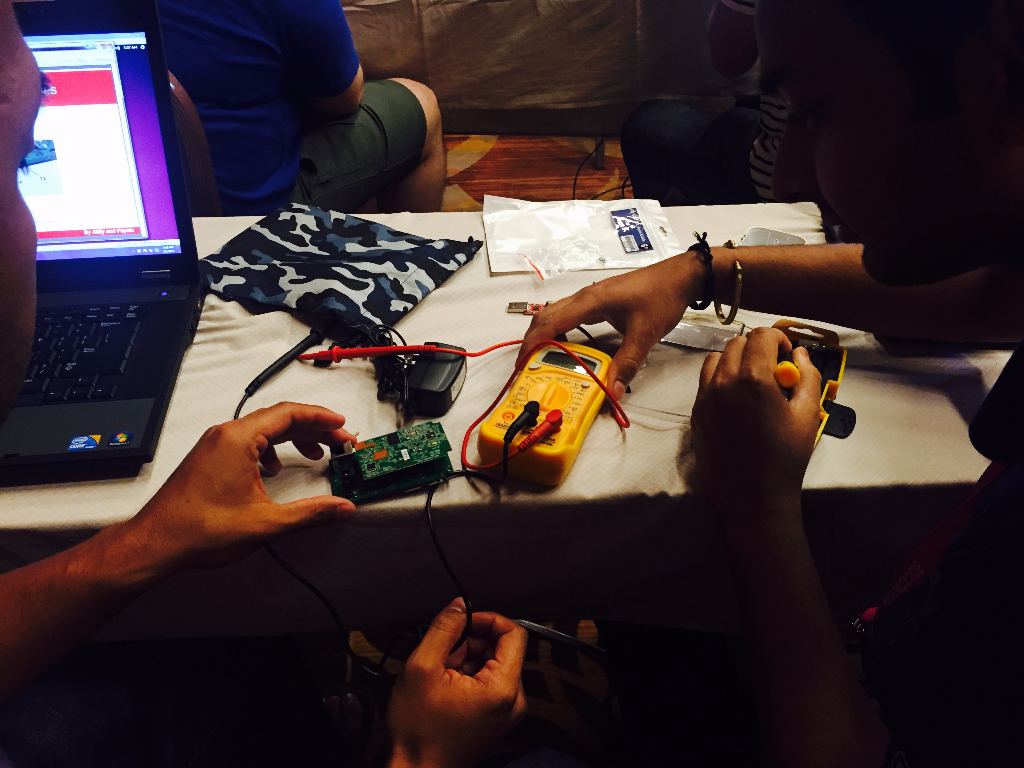
Some pictures from our class :


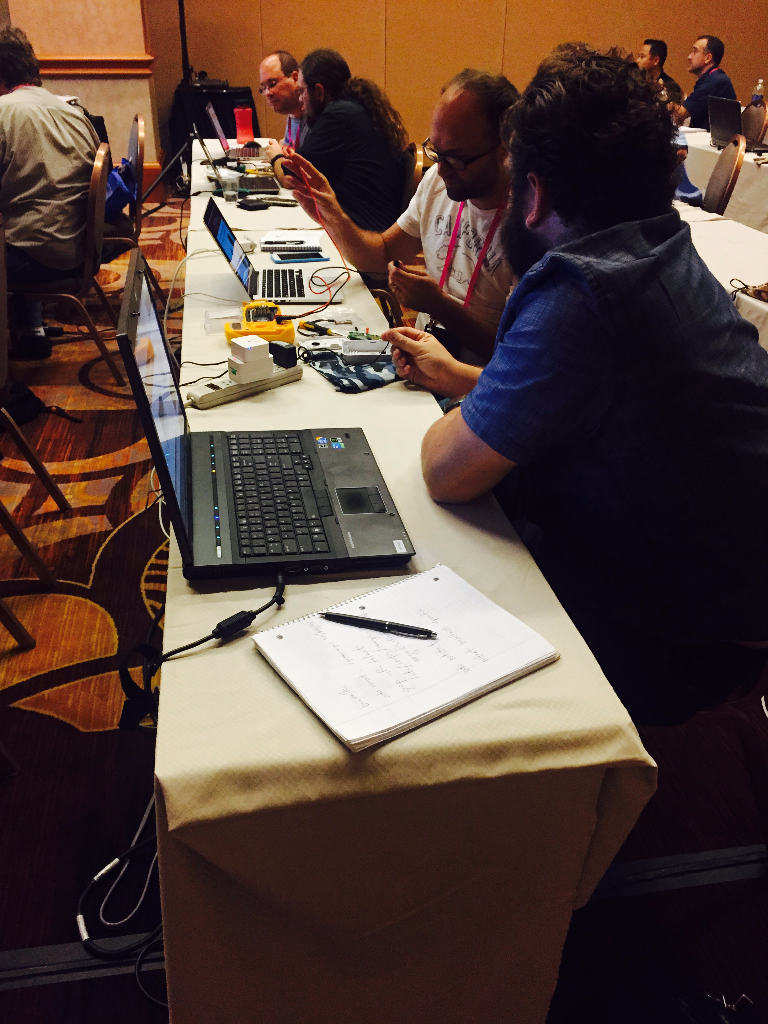
The class was divided into 3 sections :
- Embedded Device Security Analysis and Exploitation
- Mobile/Web Based vulnerabilities
- Radio Communications Security
This is indeed the 3 sections on which consists of any Internet of Things architecture – and we decided to approach the problem of IoT security in a similar fashion. Some of the topics that we will cover in our upcoming training classes are :
- IoT architecture and attack surface analysis
- ARM and MIPS based vulnerabilities
- Firmware Analysis and finding vulnerabilities
- UART, SPI and JTAGs
- Dumping firmwares from the device and bug hunting
- Modifying and Backdooring firmwares
- Security vulnerabilities in communication protocols and implementation
- Common Mobile App based security issues
We have many more upcoming classes in various security events – Brucon, BlackHat EU etc. and are also offering private versions of the training class. Contact us here to know more about our training offerings.

