In this blog post we are going to have a look at how to intercept an Android application network traffic using a proxy tool – in this case Burp Suite. Below are the things you’ll need:
- Burp Proxy – you can download a free version from here
- Rooted device/android emulator (Genymotion)
- Android SDK Tools installed (We’ll need ADB)
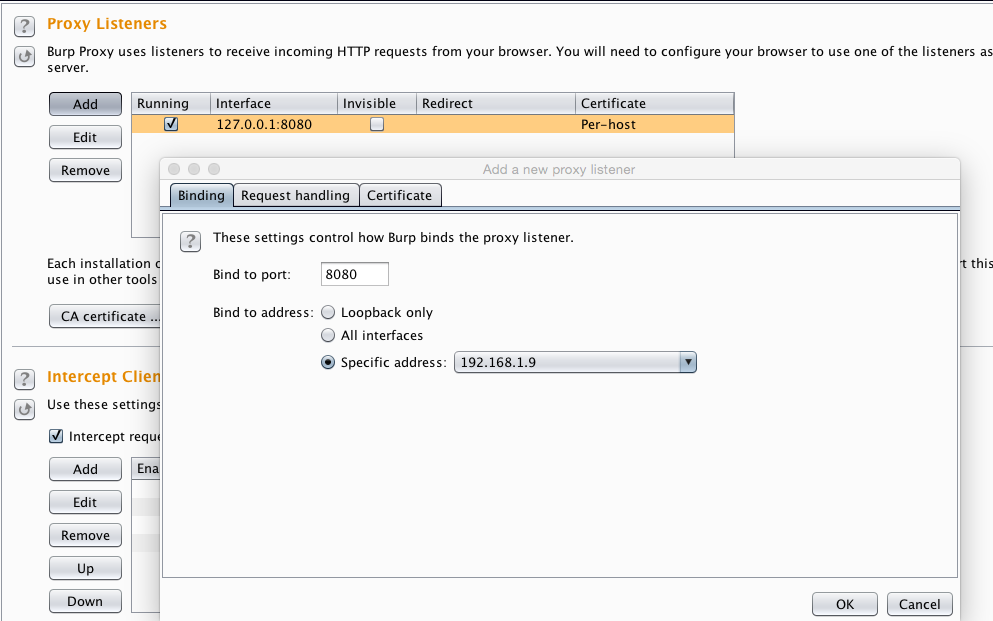
First run the burp proxy on the host machine, then click on **Proxy | Options **and in the Proxy Listener menu item, click on add interface .
Add **8080 **(or any other port for that matter where you want to capture the traffic) in the **Bind to port **option. This is simply a port number where the Burp proxy will be listening for the network traffic coming from the Android device.
In “Bind to address select simply select “Specific address” and in drop down menu select an ip address which is assigned to your host machine by virtual-box which is 192.168.1.9 in my case and click on OK
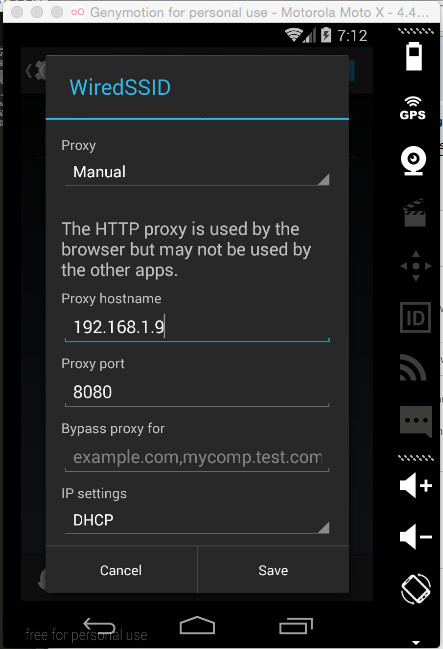
Start the android emulator (I am using android api version 4.4.4 KitKat in Genymotion)
After starting an android emulator, go to settings->WiFi then click and hold the active wifi connection and select modify network.
click on “Show advanced options” and in proxy (by default it is set to none) click on the drop down menu and select manual and now you should see more options like Proxy hostname and proxy port.
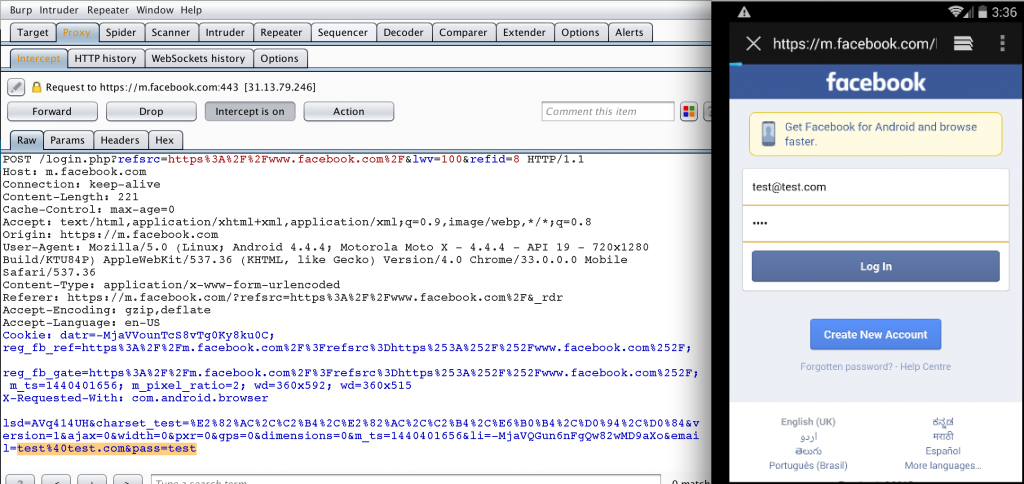
In the host name put the IP address of the Host machine where the burp is listening in my case it was 192.168.1.9 and port number was 8080 (port to which burp proxy is binded) and click on Save and now you will be able to intercept all the “HTTP” (unencrypted) traffic that is sent by the android applications.
But now a days most of the android application transmits data over SSL which you cannot normally intercept using the above step. So to intercept the SSL traffic you need to import a CA certificate (of your host machine proxy which will be intercepting the android traffic) to the android keystore.
To do this you need to perform additional steps given below:
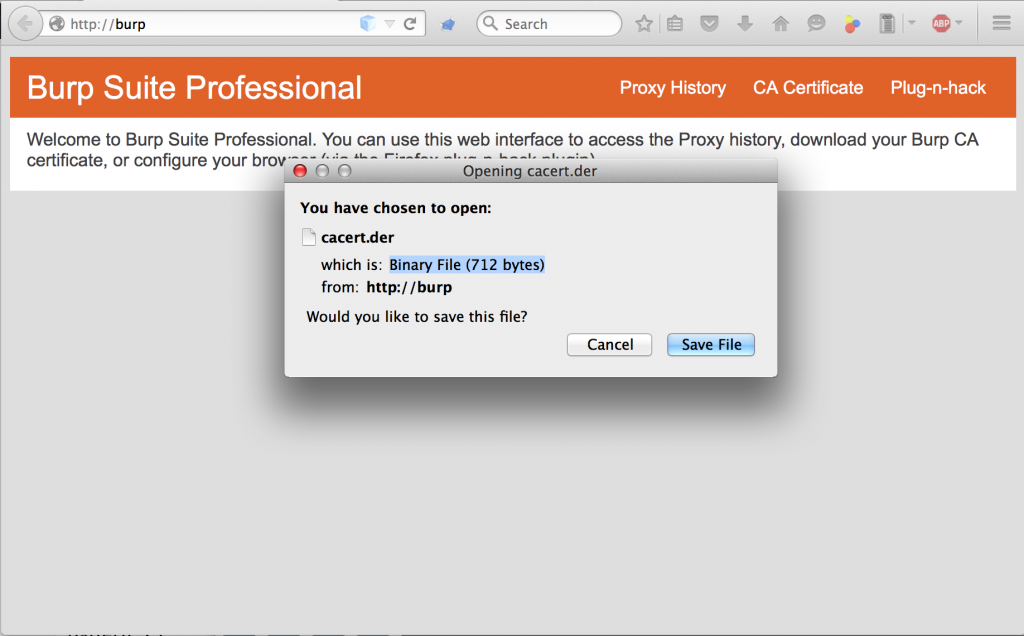
- change the proxy setting in the browser and set the host to 127.0.0.1 and port to 8080 then go to http://burp/ and click on CA Certificate and it will download a CA certificate.
-
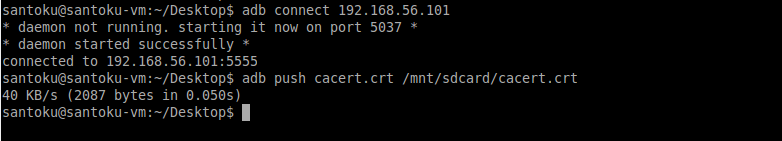
Rename the CA certificate to cacert.crt and push it to the emulator SDCARD using the following commands:
-
adb connect 192.168.56.101 2. adb push cacert.crt /mnt/sdcard/cacert.crt
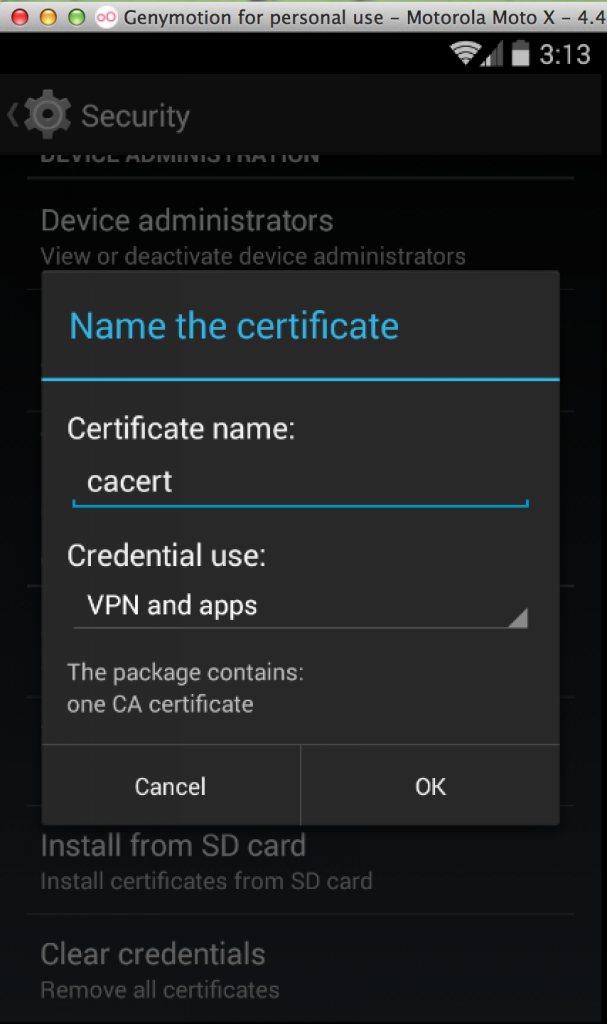
- Now in the emulator / device go to “Settings->Security” in the Credential storage select “Install form SD Card” and then you can select the “cacert.crt” file present in the sd card and give the name cacert and click on ok and it will ask you to set a lock screen click on ok and select a type of lock screen and confirm (don’t forget the lock screen pattern)
And thats it! Now you will be able to intercept the SSL traffic of the android applications.
Is this the end ?? No.
Now a days most of the critical applications use a mechanism used SSL pinning.
What is SSL Pinning?
SSL pinning is basically checking if the server certificate matches with the certificate in the application. If not then it will give you an error and you wont be able to intercept the traffic.
By default when making an SSL connection, a client checks that the server’s certificate:
- Has a verifiable chain of trust back to a trusted (root) certificate.
- Matches the requested domain name.
Most of the developers wont implement proper SSL pinning mechanism which would sometime allow us to bypass the SSL Pinning mechanism by patching the instances where SSLPinning is implemented.
Another simple method to bypass SSL pinning is by Using a tool called “Android TrustKiller” developed by iSECPartners.
This tool uses Cydia Stubstrate to hook various methods in order to bypass certificate pinning by accepting any SSL Certificate.
To use this tool first you need to install
- Cydia Substrate available in android play store.
- Then Install apk available in Android TrustKiller
After installing Cydia Substrate and Android TrustKiller open Cydia substrate and select “Link Substrate files” and thats it ! now you will be able to intercept the SSL traffic even if SSL Pinning is implemented.