We just completed the training at BlackHat Asia 2016.
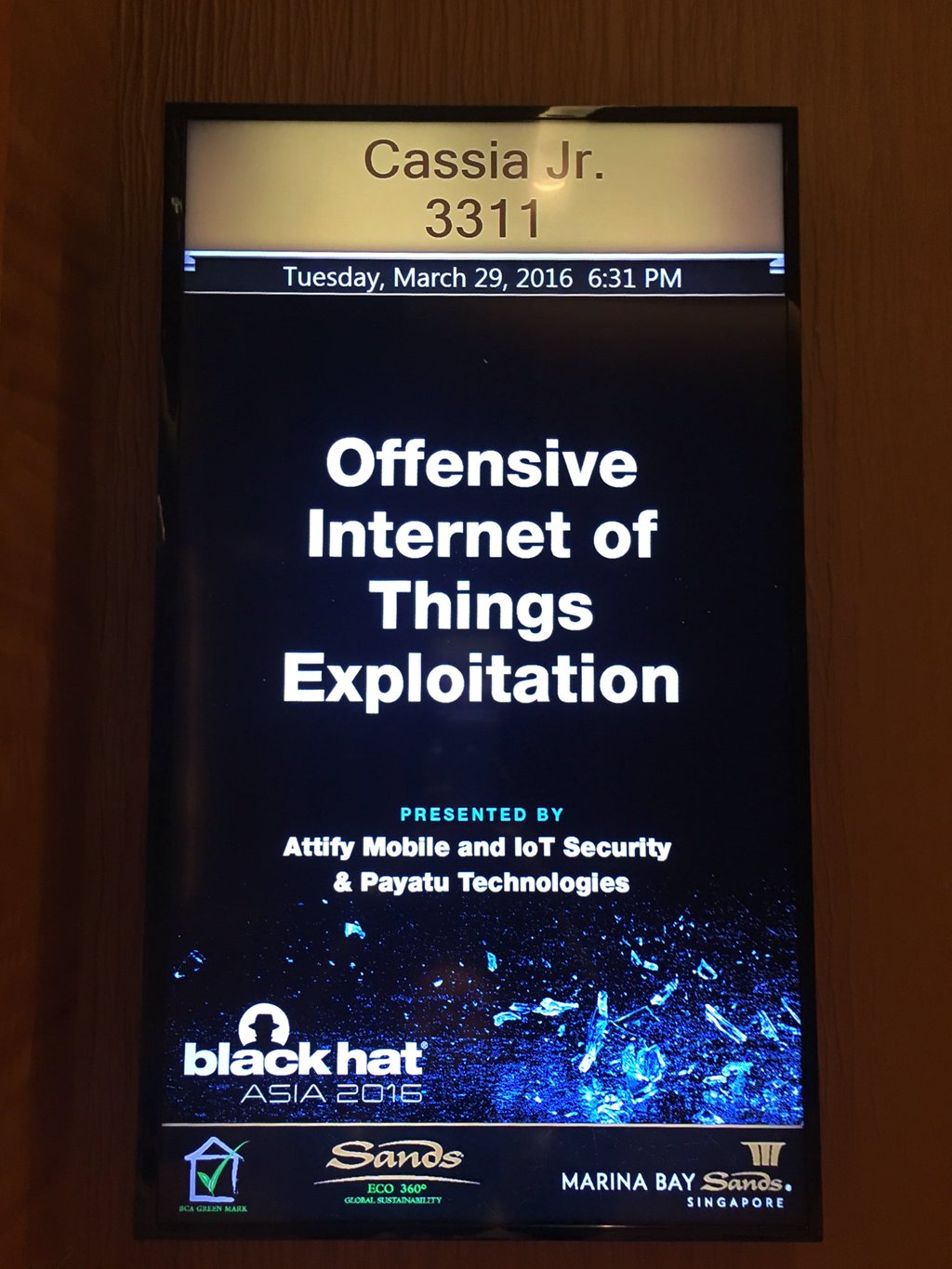
BlackHat Asia : Attify’s training on IoT Exploitation (Pic credits : gpheheise )
Like almost any other major security conference, this time at BlackHat Asia 2016 , Attify was present to interact with its existing clients and also to conduct a security training and contribute to a panel discussion.
This time at BlackHat Asia 2016, Attify conducted a hands-on technical training session on Offensive Internet of Things Exploitation, which is a flagship course offered by Attify. The course was a major hit (as expected) just like in BlackHat USA 2015 and several other conferences.
We are also revamping our training offerings and the overall agenda for this year. Keep an eye out on the training page for more info. Apart from the training offering at BlackHat, Attify’s CEO – Aditya Gupta was also a member of panel discussion organised by Dark Reading to discuss about the impact of Internet of Things, and how vendors could create safer *smart *things.
The conference had some really great talk lineup such as Bypassing Browser Security Policies for Fun and Profit, where Rafay Baloch discussed about vulnerabilities in SOP for the Android platform/apps, CANtact tool presentation by Eric for hacking automotives, Automated Dynamic Firmware Analysis at Scale by Andrei etc.
Overall, it was a great experience with great talk, training and events lineup. In case you couldn’t make it to Attify’s training at Asia, feel free to get in touch with us at secure@attify.com for a training at your organisation.
