A lot of new IoT ( **Internet of Things **) and smart devices are coming up every now and then, and being a user myself, I thought a few basic and handy tips will be useful to the community, in order to ensure the security of your data and device.
IoT being a new and emerging market, there is not enough security awareness among the developers and companies who create the products. So here are some tips for the users :
Always Change the Admin Login credentials
If you buy a Smart Hub (which is a great example – Internet of Things or IoT Device) or a smart medical device, chances are there will be an option to change the default password/pin credentials. Go through the manual and change the default login credentials as soon as you get the device.
It is one of the most important things which can protect you from hackers getting access to your device and data. Default password is the first attempt for an attacker to breach your security.
Ensure to go through the privacy and security settings of the Internet of Things device and the connected app
I am sure when you got that the new iPad or downloaded that new app, you went through its settings. In the same way, go through the Settings of your IoT device and have a look at the current security settings. Disable the option that you think might not be useful for you and could be a risk for your privacy. .
If you want your IoT enabled baby monitor cam to periodically click a picture of your baby, which is fine but do you also want your baby monitor to publish those pictures in the cloud, reducing the security of the pictures by a significant level?
Another example, if you want your new IoT enabled running shoes to keep track of your miles, which is good, but you might not want to share all your running details to your Twitter feed, allowing your followers to have a track of you.
So, in conclusion, disable the features which you think is not necessary to you and might be an invasion of your privacy. This is one of the highly recommended ways in which you can secure your Internet of Things or connected device.
Make sure the IoT device is always up to date with the latest firmware and software updates
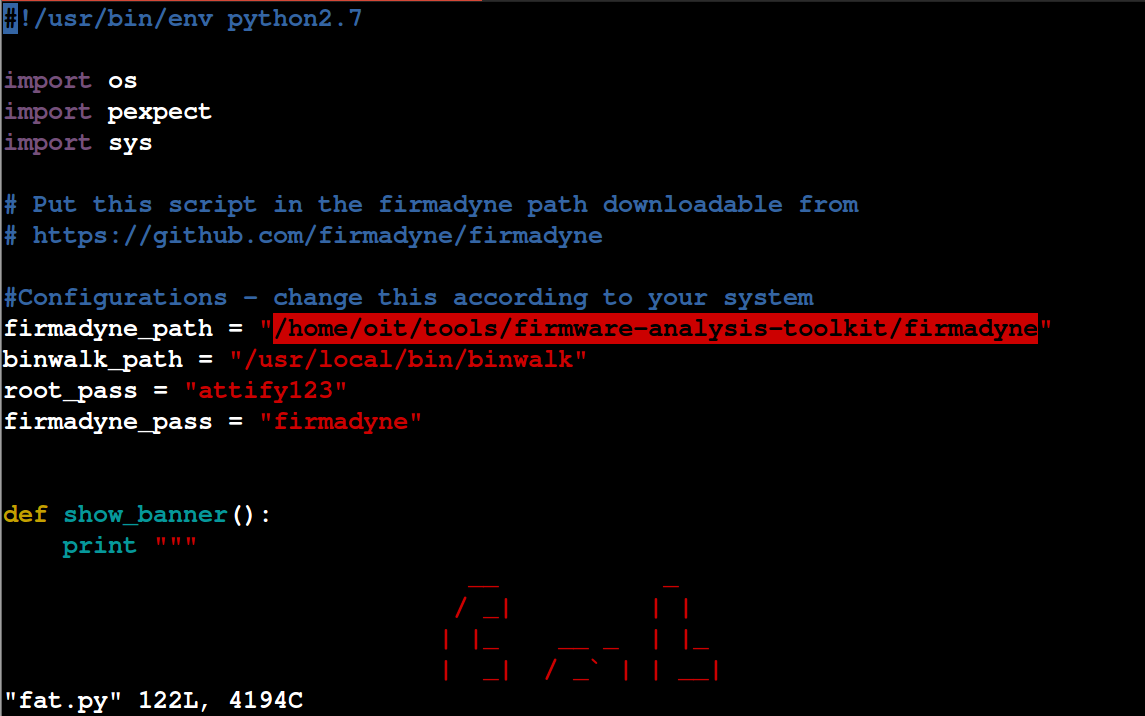
Security Researchers and attackers keep on identifying vulnerabilities in variousSmart and IoT devices. It’s tough to keep a track of all the security issues identified, and applying a security fix yourself. Chances are, your Smart Device manufacturer is aware of the security vulnerabilities, and patches it by releasing a new update to either the device firmware or mobile app.
By applying all the latest firmware and software updates by your device manufacturer, you will be protected against a lot of publicly released security issues for your device.
These were some of the tips which a user can do to protect his identity, and ensure security for his/her smart devices.
Stay safe and secure.
**About Attify: **
Attify is a leading provider of Mobile, Web and IoT Security solutions for the enterprises.
We provide 360 degree security assessment of IoT devices. Along with security auditing, we also provide training on Offensive IoT Exploitation.
You can also contact us using the form below for details on** Mobile Application Security**, Security Training or** IoT Device Pentesting** :
[contact-form][contact-field label=’Name’ type=’name’ required=’1’/][contact-field label=’Email’ type=’email’ required=’1’/][contact-field label=’Query’ type=’textarea’ required=’1’/][/contact-form]